How to Implement Basic Cybersecurity
How to implement basic cybersecurity represents a critical investment for organizations of all sizes in our increasingly connected digital landscape. Cyber attacks have escalated dramatically, with 43% targeting small businesses despite their limited resources. The good news: you don’t need massive budgets or advanced expertise to establish strong foundational security. This comprehensive guide walks you through implementing effective cybersecurity measures using proven frameworks and practical strategies.
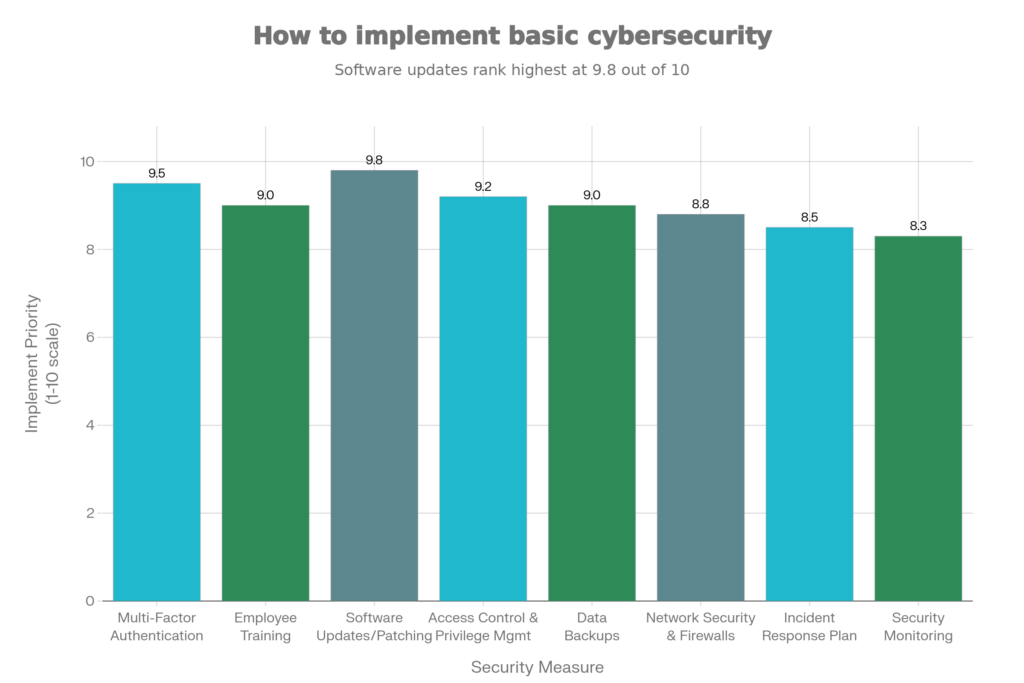
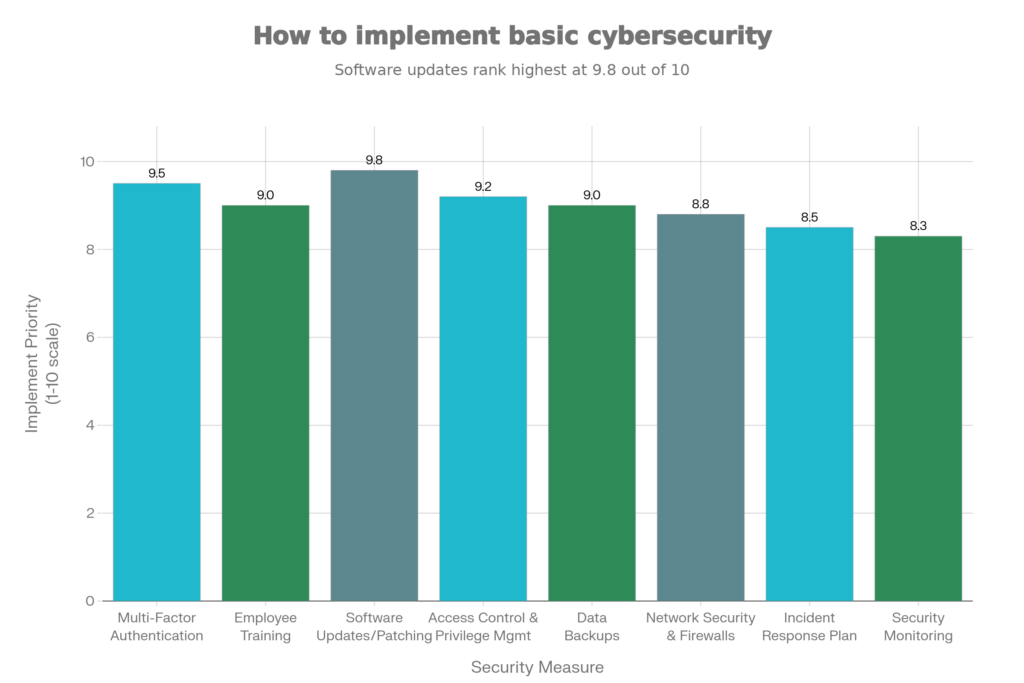
Organizations worldwide recognize that how to implement basic cybersecurity determines their resilience against evolving threats. Data breaches increased 600% during recent years, with ransomware demands averaging $572,000. However, implementing straightforward protective measures significantly reduces breach likelihood and impact. The following eight-step framework provides a actionable roadmap for establishing security foundations regardless of organizational size.
Understanding How to Implement Basic Cybersecurity Fundamentals
Why Cybersecurity Matters Now
How to implement basic cybersecurity starts with recognizing genuine risks. Threat actors target businesses indiscriminately, recognizing that small organizations often lack adequate defenses. Regulatory requirements (HIPAA, PCI-DSS, GDPR) impose substantial fines for negligent data protection. Customer trust depends on demonstrating security commitment. Therefore, treating cybersecurity as non-negotiable business priority, not optional expense, proves essential.
Furthermore, how to implement basic cybersecurity protects more than data—it ensures operational continuity. Ransomware attacks disable critical business functions costing organizations millions in downtime. Business email compromise schemes redirect funds to criminals. Phishing campaigns install malware across networks. These attacks inflict immediate operational and financial damage.
The Role Of Frameworks
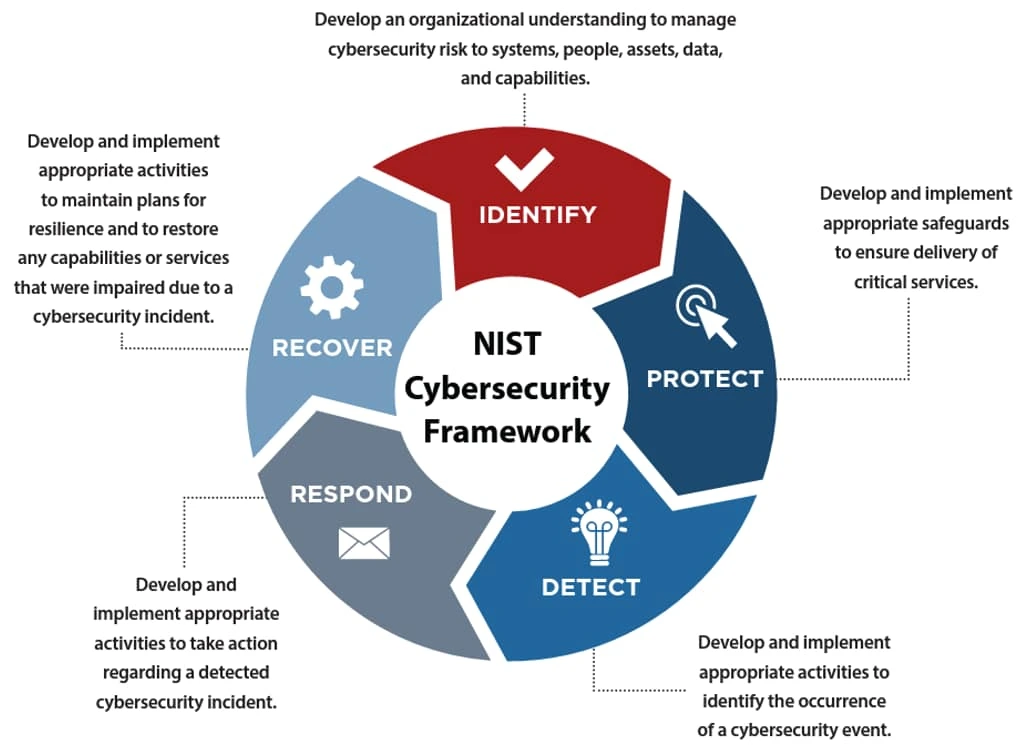
Fortunately, how to implement basic cybersecurity doesn’t require inventing custom approaches. Established frameworks like NIST Cybersecurity Framework, ISO 27001, and CIS Controls provide proven blueprints. These frameworks emerged from decades of industry experience, capturing best practices across diverse organizations. The NIST framework specifically organizes cybersecurity into five core functions: Identify, Protect, Detect, Respond, Recover.

- Select options This product has multiple variants. The options may be chosen on the product page
- USD: $ 116.65 - $ 833.32
- USD: $ 6.65

- USD: $ 499.98

- Select options This product has multiple variants. The options may be chosen on the product page
- USD: $ 8.32 - $ 83.32

- USD: $ 8.32

- Subscribe Now This product has multiple variants. The options may be chosen on the product page

- Subscribe Now This product has multiple variants. The options may be chosen on the product page

- Subscribe Now This product has multiple variants. The options may be chosen on the product page

- Select options This product has multiple variants. The options may be chosen on the product page
- USD: $ 99.98 - $ 833.32

- Select options This product has multiple variants. The options may be chosen on the product page
- USD: $ 199.98 - $ 999.98
8-Step Framework: How to Implement Basic Cybersecurity
Step 1: Conduct Security Risk Assessment
The foundation of how to implement basic cybersecurity involves understanding what you’re protecting and from whom. Conduct a thorough risk assessment identifying all organizational assets—hardware, software, data, cloud services.
Assess vulnerabilities systematically. Where could attackers gain unauthorized access? What data would cause maximum damage if compromised? Which employees handle sensitive information? Document findings in a risk register prioritizing high-impact, high-likelihood threats.
Step 2: Set Clear Security Goals
How to implement basic cybersecurity requires alignment with business objectives. Security goals should directly support organizational success, not exist in isolation. For instance, a retail business prioritizes protecting customer payment data (PCI compliance), while healthcare organizations focus on patient information (HIPAA).
Involve leadership in goal-setting discussions. Executive commitment proves essential for resource allocation and policy enforcement. Set realistic timelines, allocate budgets honestly, and establish measurable success metrics.
Step 3: Evaluate Current Technology
Understanding your existing technology landscape is crucial for how to implement basic cybersecurity effectively. Catalog all systems, applications, operating systems, and infrastructure components. Identify outdated, unsupported software no longer receiving security patches.
Assess how data flows through your environment. Where is sensitive information stored? Who can access it? How is it transmitted across networks? Document this infrastructure thoroughly—you cannot secure what remains invisible to your team.
Step 4: Select Appropriate Security Framework
How to implement basic cybersecurity benefits enormously from established frameworks providing structured guidance. NIST works exceptionally well for smaller organizations beginning their security journey. CIS Controls offers eighteen straightforward practices addressing primary threat vectors.
Choose frameworks aligned with your regulatory environment and industry requirements. Healthcare organizations benefit from HIPAA-specific frameworks, while government contractors require CMMC compliance. Don’t over-complicate—most small businesses succeed with NIST’s five core functions.
Step 5: Review And Develop Security Policies
How to implement basic cybersecurity requires documented procedures employees actually follow. Develop policies covering these critical areas: acceptable use of company systems, data classification and handling, password requirements, remote access, incident reporting, and breach response.
Keep policies accessible and understandable. Long, complex policy documents get ignored. Instead, create concise, specific procedures employees can reference easily. Include consequences for violations—enforcement demonstrates genuine commitment.
Step 6: Create Risk Management Plan
Moving beyond assessment toward mitigation is essential in how to implement basic cybersecurity successfully. Develop specific strategies addressing each significant risk. For phishing threats, implement employee training and email filtering. For ransomware, establish automated backups stored offline.
Prioritize remediation efforts realistically. Address critical vulnerabilities first, handling lower-risk items incrementally. Set timelines balancing urgency with practical implementation capability.
Step 7: Implement Your Cybersecurity Strategy
Now execute your carefully developed plan. How to implement basic cybersecurity at this stage requires coordinated deployment across your organization. Assign responsibilities clearly—who handles infrastructure changes, who manages users, who conducts training?
Use project management approaches ensuring accountability. Set realistic deadlines, communicate progress regularly, celebrate milestones. Avoid aggressive timelines that guarantee failure—better to exceed modest expectations.
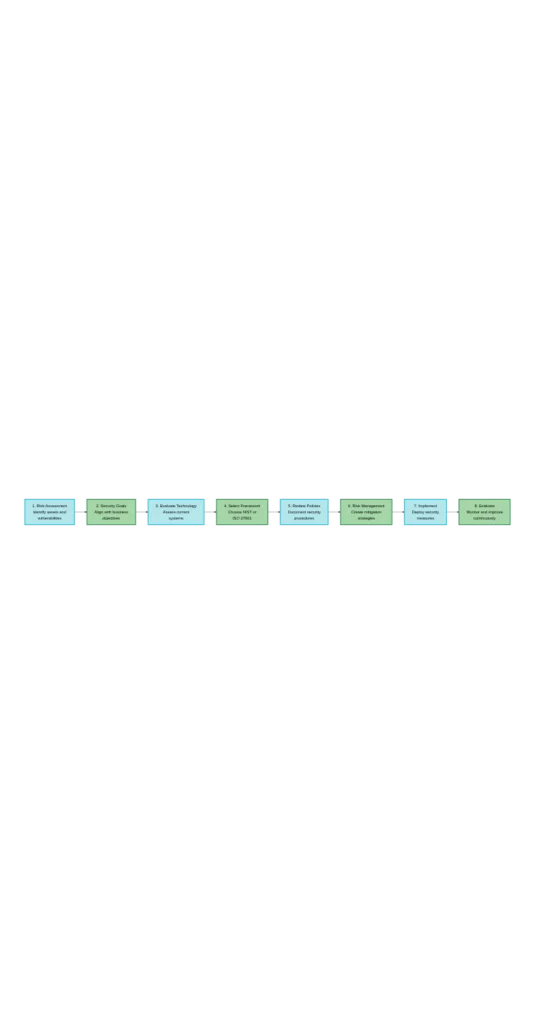
Step 8: Evaluate, Monitor, And Improve Continuously
How to implement basic cybersecurity isn’t a one-time project but ongoing process. The threat landscape evolves constantly, requiring continuous adaptation. Establish annual review cycles examining your security posture against current threats.
Monitor systems actively for suspicious activity using logs and alerts. Conduct regular vulnerability scans identifying newly discovered weaknesses. Perform penetration testing validating your defenses work as intended.
Key Security Measures For Basic Implementation
Multi-Factor Authentication (MFA)
MFA dramatically reduces unauthorized access risk by requiring additional verification beyond passwords. Even if attackers compromise credentials, they cannot access protected systems without second factors like smartphone codes. Prioritize MFA for email, administrative access, and systems handling sensitive information.
Employee Security Training
IBM research shows 90% of cyber attacks involve human error. Comprehensive employee training transforms your staff from security liabilities into frontline defenses. Cover phishing recognition, password practices, physical security, and reporting procedures.
Software Updates And Patch Management
Outdated software harbors known vulnerabilities attackers actively exploit. Establish automated update processes—critical security patches should deploy within days of release. Test updates before deployment, but never delay implementation indefinitely.
Strong Access Controls
The principle of least privilege ensures users only access information essential for their roles. Restrict administrative access severely, removing unnecessary permissions regularly. Monitor access logs for unusual activity indicating compromised accounts.
Cost-Effective Implementation Strategies
Leverage Free And Low-Cost Tools
How to implement basic cybersecurity doesn’t require expensive enterprise solutions. Free tools like OpenSSL encryption, community firewalls, and password managers provide genuine protection. Microsoft Defender for Business costs only $3/user/month—affordable for small businesses.
Start With High-Impact Measures
Prioritize activities delivering maximum security improvement per dollar spent. Multi-factor authentication, employee training, and patch management require modest investment but dramatically increase security.
Use Cloud Provider Security Features
Most cloud platforms include built-in security features—enable them all. Encryption, access controls, monitoring, and backup services included with cloud subscriptions shouldn’t be ignored.
Partner With Service Providers
If internal expertise is lacking, managed security service providers (MSSPs) handle monitoring, threat response, and compliance. This approach proves especially viable for small businesses lacking dedicated security staff.
Youth Co:Lab 2026 Innovation Challenge – Get Upto ₹3.5 Lakh
Responsible Consumption Innovation Challenge - Atal Innovation Mission (AIM), NITI Aayog, in partnership with UNDP India and Citi Foundation, implemented by T-Hub Foundation.
₹350,000.00- Idea Stage, Prototype Stage, MVP Stage, Early Revenue Stage
- March 20, 2026
Execution Strategies For Sustainable Growth
Lean Launch Philosophy
Successful business under 50000 operations adopt lean launch principles: minimize upfront investment, validate market demand through small-scale testing, scale only after proving viability. Rather than purchasing ₹50,000 inventory immediately, test with ₹5,000 worth, gather customer feedback, then expand intelligently.
Customer Satisfaction Focus
Moreover, a business under 50000 thrives through relentless customer satisfaction. Quality products, reliable delivery, responsive communication, and fair pricing build loyalty and referrals. Each satisfied customer becomes a marketing channel, reducing customer acquisition costs for capital-constrained ventures.
Reinvestment Strategy
Furthermore, reinvest profits back into business under 50000 operations rather than personal consumption. This growth capital accelerates expansion: better equipment, improved inventory, additional staff, enhanced marketing. Many successful entrepreneurs reinvest 70-80% of profits annually during growth phases.
Conclusion
How to implement basic cybersecurity successfully combines strategic planning, foundational security measures, employee commitment, and continuous improvement. The eight-step framework—from risk assessment through continuous monitoring—provides organizations of any size with proven implementation guidance. You don’t need massive budgets or PhD-level expertise to establish effective defenses that meaningfully reduce breach likelihood and impact.
At StartupMandi, we recognize that how to implement basic cybersecurity represents a fundamental challenge for growing organizations. Explore our complete cybersecurity implementation roadmap providing step-by-step guidance for each framework stage. For entrepreneurs concerned about protecting customer data and intellectual property, our detailed security measures guide breaks down practical approaches matching various organizational sizes and budgets.
Additionally, StartupMandi provides specialized cybersecurity consulting for founders seeking expert guidance on regulatory compliance, threat assessment, and cost-effective security investments. Connect with our [cybersecurity advisory team] to develop customized security strategies aligned with your business model and growth stage. Moreover, explore our [vendor security assessment guide] ensuring third-party partners meet your security standards.
Frequently Asked Questions
Q1: How much does it cost to implement basic cybersecurity?
A: Costs vary dramatically by organization size and maturity. Small startups implementing foundational measures spend $1,000-$5,000 annually. Mid-sized companies typically invest $50,000-$200,000 yearly. The key insight: cybersecurity implementation costs far less than recovering from data breaches, which average $4.29 million in damages including notification, legal fees, and business disruption.
Q2: Which cybersecurity framework should small businesses use?
A: NIST Cybersecurity Framework works exceptionally well for smaller organizations because it’s flexible, non-prescriptive, and provides clear guidance without overwhelming complexity. CIS Controls offers simpler starting points with eighteen specific practices. ISO 27001 suits organizations requiring formal compliance certification. Most small businesses succeed starting with NIST or CIS frameworks.
Q3: How long does basic cybersecurity implementation take?
A: Basic implementation typically requires 2-6 months for small organizations with limited complexity. Large enterprises may require 1-3 years. The timeline depends on current security maturity, organizational size, and complexity. Better to implement thoughtfully than rush processes, ensuring employees understand and follow security procedures.
Q4: Should we hire a Chief Information Security Officer (CISO)?
A: Small startups typically don’t need full-time CISOs. Instead, appoint a security-focused leader responsible for cybersecurity initiatives and reporting to executive leadership. Larger organizations (100+ employees) benefit from dedicated CISO roles. Many small businesses hire fractional CISOs or consultants providing part-time oversight at reasonable costs.
Q5: How do we measure cybersecurity implementation success?
A: Track key performance indicators including percentage of systems running current patches, multi-factor authentication adoption rates, employee security training completion, successful phishing simulation resistance, mean time to detect threats, and mean time to respond. Regular security assessments verify controls function as intended. Annual risk assessments should show declining overall risk exposure.
Referring Blog & Page Links
Inbound Links (Internal – StartupMandi):
- How to build Ecommerce Business India: Your Complete Launch Guide
- How to Register Private Limited Company In India – Step by Step Guide
- Refund and Returns Policy
- Profitable AI Startup Ideas for 2026
- Business Under 50000: 7 Profitable Ideas to Start
Outbound Links (External – Authority Sources):

Mariyam Bandookwala
i am a professional content writer with a strong focus on clarity, strategy, and audience engagement—helping brands communicate smarter and grow faster.